There are roughly 6,000 internet-accessible Palo Alto Networks firewalls potentially affected by a recently addressed exploited vulnerability, the Shadowserver Foundation reports.
Palo Alto Networks disclosed the flaw on April 12 and started rolling out patches a couple of days later. The issue had been targeted by state-sponsored threat actors and its exploitation surged last week, as proof-of-concept (PoC) code was published.
The issue, tracked as CVE-2024-3400 (CVSS score of 10/10), is described as a command injection in the GlobalProtect feature of PAN-OS, the operating system running on Palo Alto Networks’ appliances.
According to the vendor’s updated advisory, the flaw is rooted in an arbitrary file creation defect and, under specific conditions, can be exploited without authentication to execute arbitrary code with root privileges on a vulnerable firewall.
Initially, Palo Alto Networks said that only appliances with the GlobalProtect gateway feature configured and device telemetry enabled are vulnerable, and recommended disabling device telemetry as a mitigation.
The revised version of the advisory, however, removes the device telemetry mentions and points out that disabling the feature is no longer considered an effective mitigation.
“Device telemetry does not need to be enabled for PAN-OS firewalls to be exposed to attacks related to this vulnerability,” the vendor notes.
In an April 19 blog post, Palo Alto Networks explained that CVE-2024-3400 was rooted in two PAN-OS flaws leading to unauthenticated remote shell command execution when combined.
The first bug existed because the GlobalProtect service failed to sufficiently validate the session ID format before storage, allowing an attacker to send a crafted shell command and create an empty file with an embedded command as the filename.
The second issue was that the OS trusted that the file was system-generated, leading to a scheduled system job to use the filename in a command, thus executing the attacker-supplied command with elevated privileges.
While the successful exploitation of the first bug would only lead to the creation of an empty file with a specific filename, the exploitation of the second would allow attackers to steal sensitive information or deploy malware.
“A highly sophisticated threat actor discovered that by uniquely combining the two bugs, they could perform a two-stage attack to achieve command execution on the vulnerable device,” Palo Alto Networks says.
The vendor recommended disabling device telemetry as it prevented the system cron job from running, thus preventing the command execution, but later discovered additional methods of exploiting CVE-2024-3400 that did not require telemetry to be enabled.
“The fix effectively removes the two problems in code that enabled this vulnerability to manifest. First, the session IDs are sufficiently validated before being stored. Then, the code that enabled command injection was rewritten using defensive programming techniques,” Palo Alto Networks says.
The company also notes that Threat Prevention signatures released on April 11 could fully block all known suspicious patterns in session IDs, and that roughly 90% of its customers have applied the mitigation.
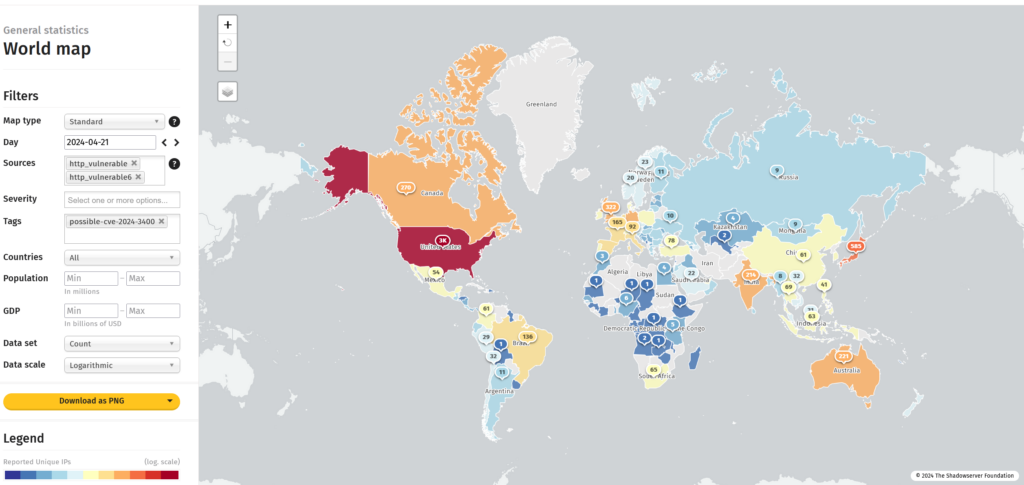
On Friday, Shadowserver Foundation said it had observed more than 22,000 potentially vulnerable Palo Alto Networks GlobalProtect instances connected to the internet. As of April 21, data from the security organization shows roughly 6,000 potentially vulnerable instances.
Related: Thousands of Ivanti VPN Appliances Impacted by Recent Vulnerability
Related: Recent Fortinet FortiClient EMS Vulnerability Exploited in Attacks
Related: Recent Zero-Day Could Impact Up to 97,000 Microsoft Exchange Servers

















